Interview with Brian Contos: Nightmare cyberattack is comparable to a natural disaster
An excerpt from Cybernews’ article, “Nightmare cyberattack is comparable to a natural disaster – interview” with Phosphorus CSO Brian Contos
Cybernews: Could you elaborate on how threat actors used trojanized PLC and HMI password crackers like Sality on industrial targets? How does that work, and what’s the point of attacking such devices?
Brian Contos: From an operational perspective, there isn’t much difference between an attack on a PLC or a traditional IT device. Like any user who might have lost a password, PLC users might try using Google to find a solution. Attackers know people will forget things and google it, and sure enough, there’s a tool online that says it will provide a crack if downloaded – but in reality, it hides malware.
Attackers distribute malware to black-hat search engine optimization (SEO). Google and other search engines will rank websites based on how many other sites point to something. If you google “Bradley Cooper,” a famous actor, and a million sites are pointing to a specific site, that’s going to rank higher than a website with only ten servers pointing to it.
Black-hat SEO works by employing a botnet. An attacker might have thousands or tens of thousands of devices saying, “go to this site if you google Bradley Cooper.” And now, suddenly, a malicious website is ranked really high. And when you go to that site, it tries to infect you with malware.
What’s interesting is that PLCs and HMIs are most commonly associated with things like oil and gas, power, and energy manufacturing. And there are a lot of things cybercriminals can do with infected manufacturing equipment. Maybe they could poison the water supply or break a pharmaceutical company’s supply chain.
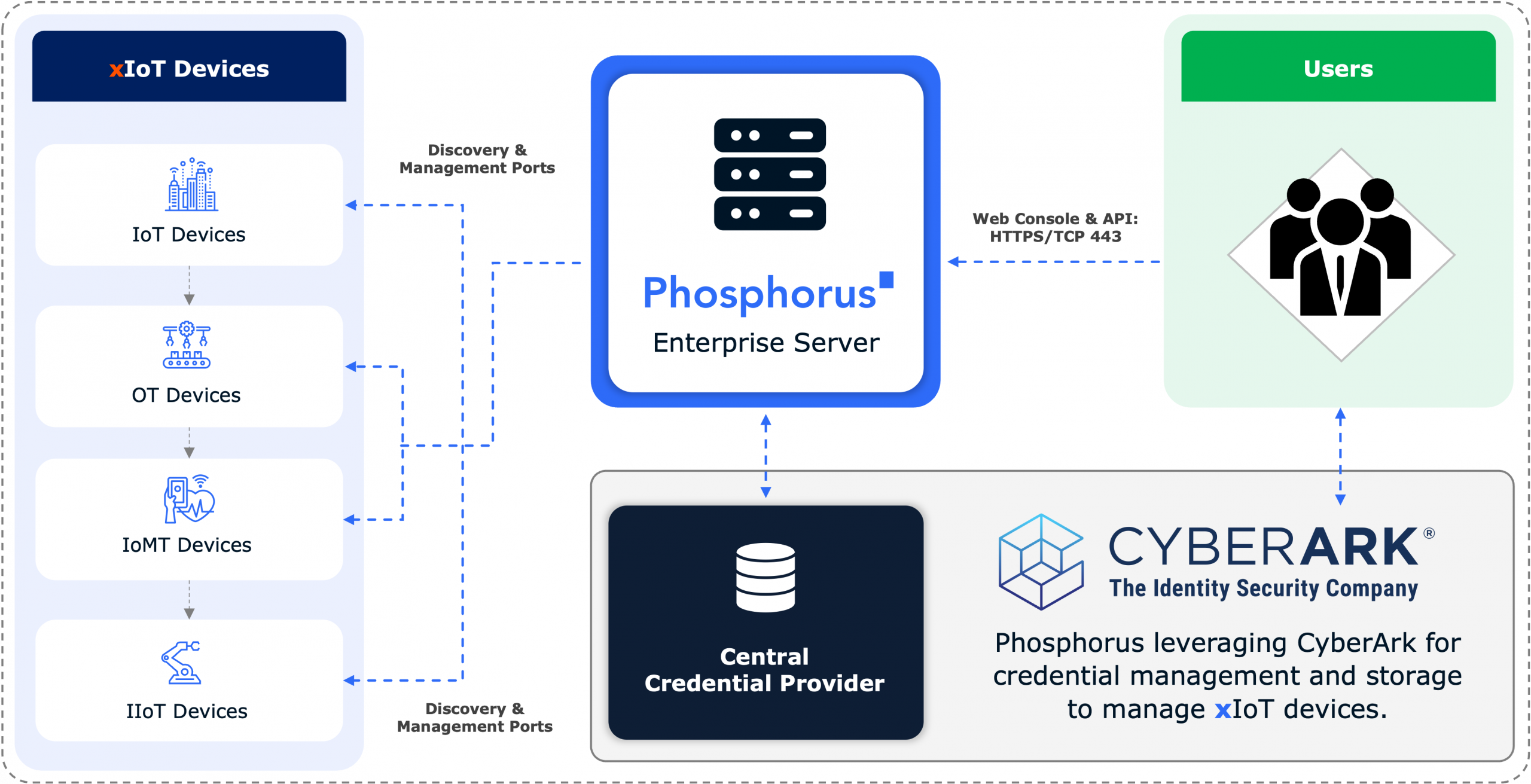
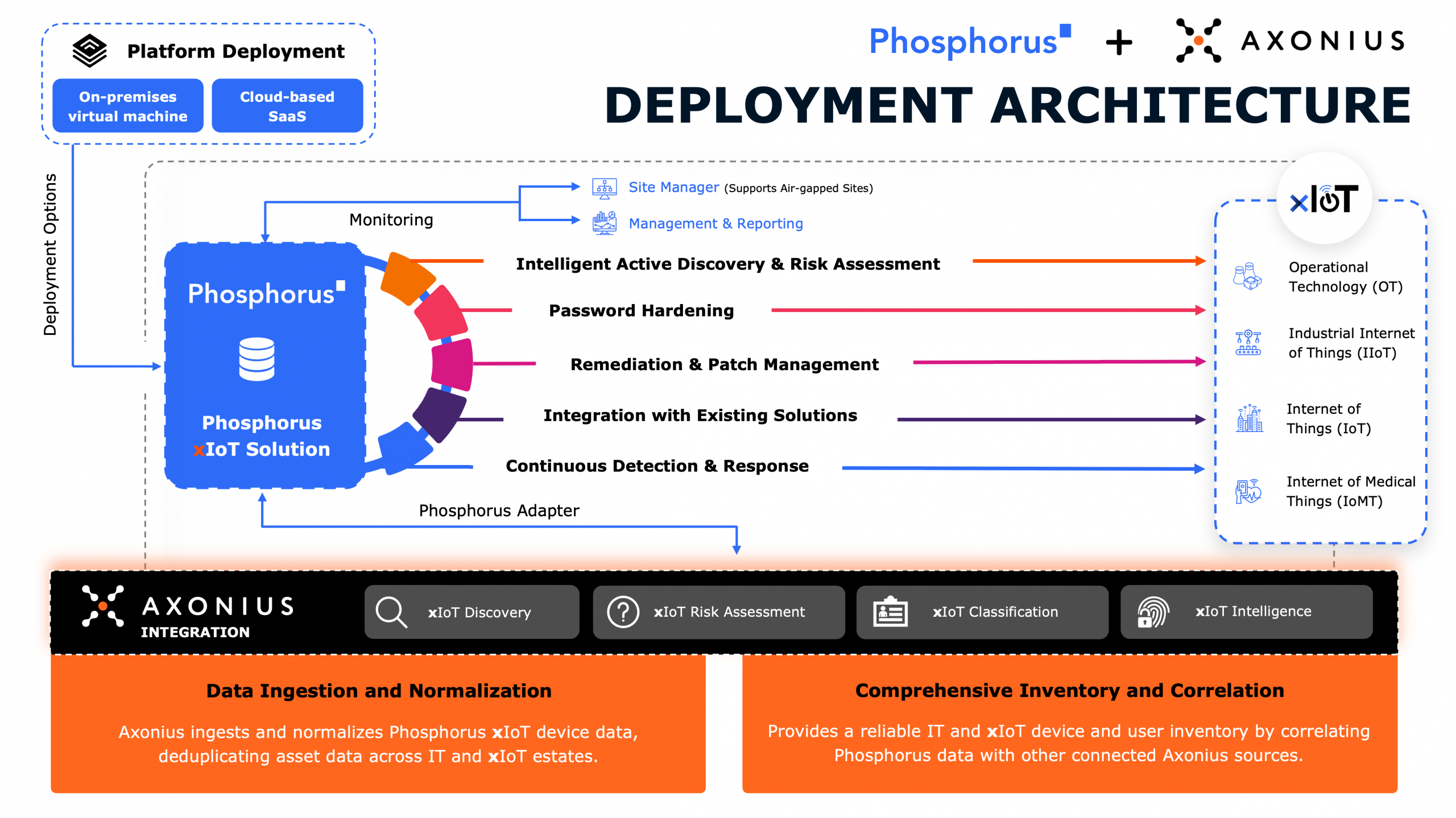
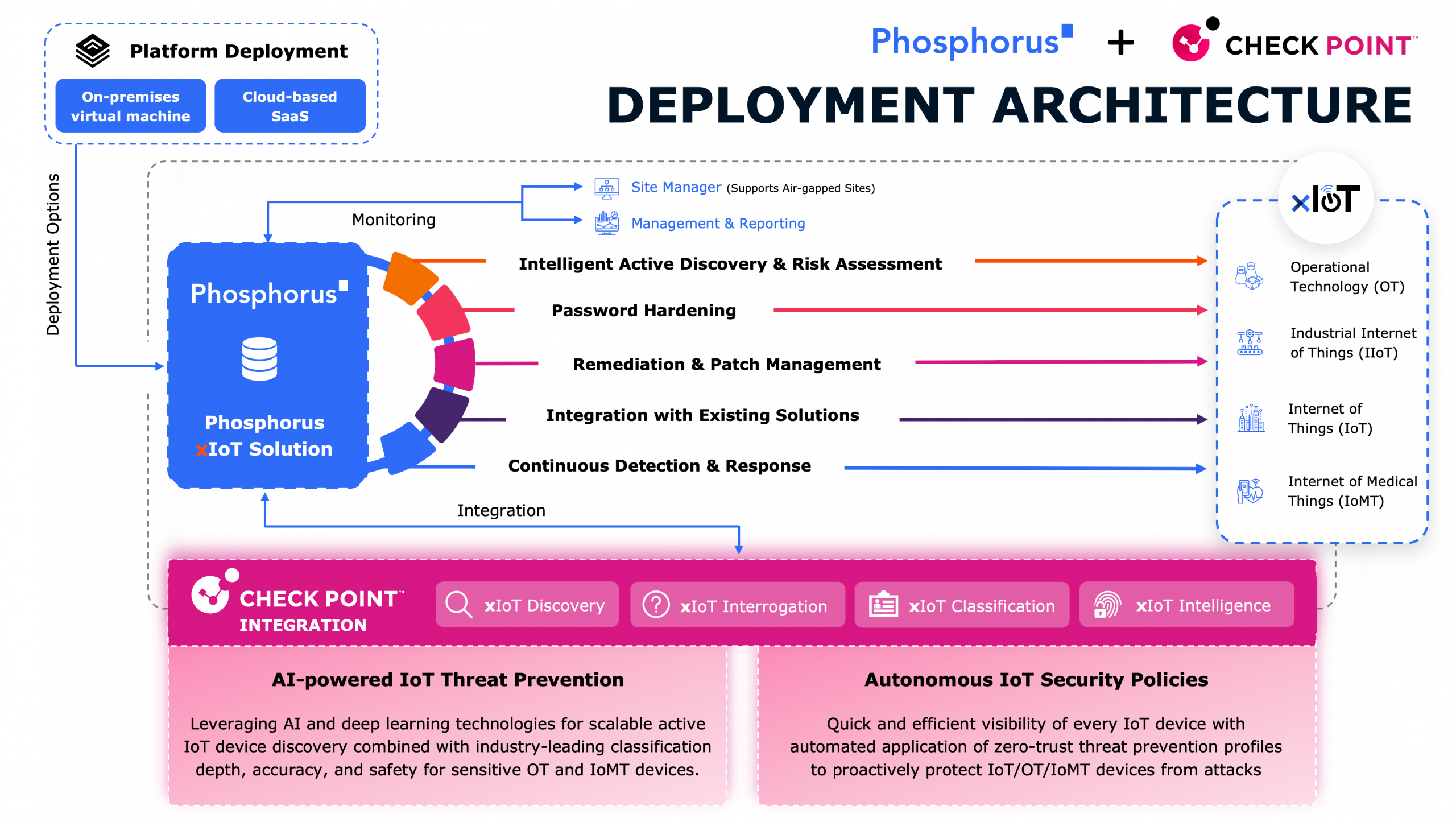
Historically, security spending was more focused on IT and less on XIoT, [which is] everything from video cameras and printers to network devices and industrial control systems. That’s becoming the new ‘new’ in cybersecurity.
There are a lot of XIoT devices, and they haven’t been secured that well. At the same time, they have the same power, capabilities, ports, and protocols as a laptop or a server, but without the pesky disadvantage of having a bunch of security controls protecting them.
***
That’s just one of the questions CSO Brian Contos answered in his interview with Cybernews. Read the full article here.
Author
Brian Contos
Chief Security Officer
With two IPOs & seven acquisitions Brian has helped build some of the most successful security companies in the world for 25+ years. He is a seasoned executive, board advisor, security company entrepreneur, author, and award-winning podcaster.