Phosphorus Cybersecurity®
Protecting xIoT Proactively and Automatically
The enterprise attack surface of today has grown beyond traditional endpoints by an order of magnitude as ~127 new xIoT devices connect to the internet every second. This creates a growing attack surface made up of billions of IoT, OT, and Network Devices, each of which have built-in identities and credentials. These critical enterprise systems are sitting ducks for hackers and nation-states to exploit.
Many enterprise xIoT devices still have default passwords in use that – if compromised – could provide attackers complete takeover of IoT systems. Needless to say, no one is walking around updating them manually. The potential impact on company valuation, brand reputation, and legal liability is catastrophic.
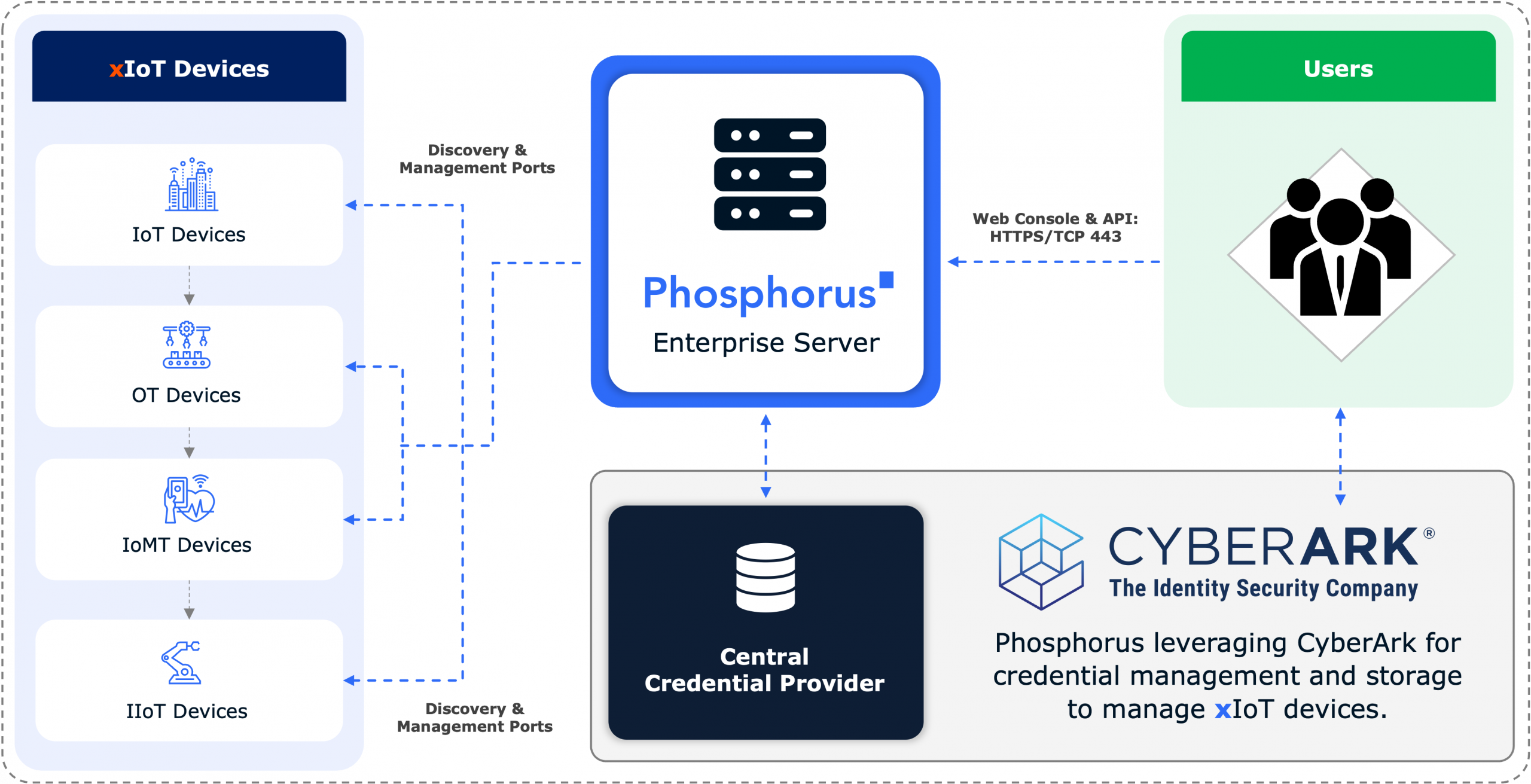
The Phosphorus integration for CyberArk reduces risk by providing comprehensive visibility and automated credential management and monitoring for enterprise IoT, OT, and network devices. Together, Phosphorus and CyberArk automate the discovery and PAM enrollment of xIoT devices and then automate credential rotation to harden the attack surface and provide a secure automated process for providing firmware updates and patches. When these tools are in place, clients can leverage CyberArk Vendor PAM to provide remote users with a secure way to authenticate to these devices without the need for a VPNs or an agent. And it’s all available out-of-the-box today.
In this webinar we will explore:
• Why credential rotation matters
• Use cases and deployment tips
• Customer success stories
• Why securing xIoT devices is so important and so powerful for enterprises
Meet the speakers:
• Brian Contos, Chief Security Officer, Phosphorous
• Brian Carpenter, Director of Business Development, CyberArk
Watch On-Demand
See Phosphorus in Action
See how you can eliminate the enterprise xIoT security gap with a live demo.