From Cheddar News: Facebook is back online after a massive global outage that affected nearly half the world’s population. Facebook, Instagram and Whatsapp were down around noon yesterday and...
In February 2017, the FBI reported that a hacker using the alias Stackoverflowin compromised over 160,000 printers by scanning for printers open on ports 515, 631, and 9100. Stackoverflowin sent...
An excerpt from the forthcoming book Practical IoT Hacking: The Definitive Guide to Attacking the Internet of Things.
From Cheddar News: The Biden administration is met with the leaders of several industry giants on Wednesday in an effort to shore up America’s protection against cybersecurity threats. Chris...
While the zero trust security model is not new, it has certainly cemented itself as cybersecurity’s hottest buzzword. Following a National Institute of Standards and Technology (NIST) and National...
An excerpt from the forthcoming book Practical IoT Hacking: The Definitive Guide to Attacking the Internet of Things.
Provider of security for IoT devices will develop solution for 5G-enabled devices.
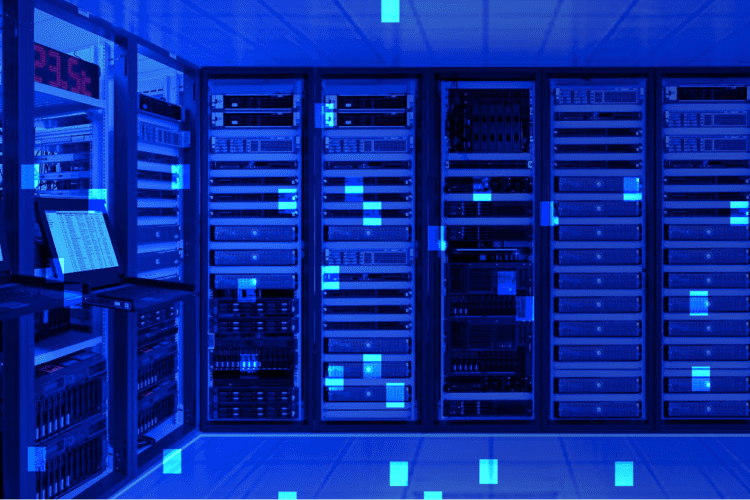
Most organizations today unknowingly leave themselves vulnerable to attack. The source of this threat: connected devices. As the number of devices connecting to the network grows, so does the...
In 2016, the makers of the Mirai malware turned their sights on well-known security expert Brian Krebs and his website KrebsonSecurity to flex their muscles. After the attackers published...
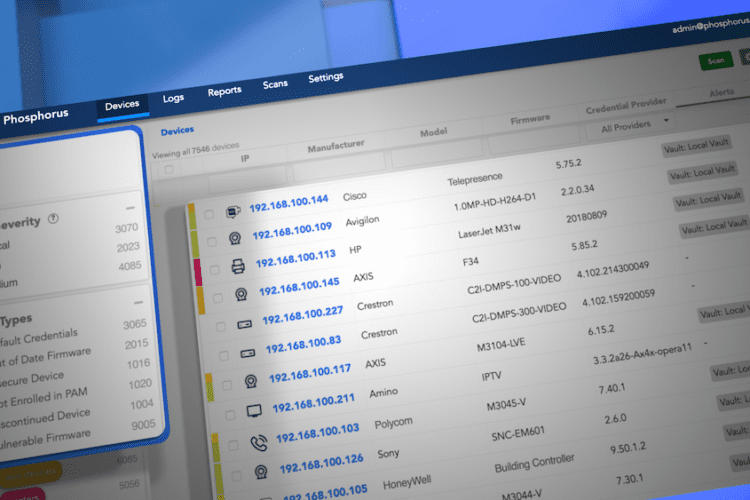
Download the Data Sheet Find Everything. Fix Everything. The Phosphorus Enterprise xIoT Security Platform enables your organization to Find, Fix, and Manage every cyber-physical asset in your enterprise. Designed...