New Partnership Will Bring the World’s Leading xIoT Attack Surface Management and Remediation Platform to the Association of Southeast Asian Nations (ASEAN) NASHVILLE, Tenn. — Phosphorus, the leading provider...
“Everything is becoming a computer… If it’s smart, it’s vulnerable.” – Mikko Hypponen, Chief Research Officer at F-Secure The enterprise attack surface of today has quickly evolved beyond traditional...
InfoSec Live founder Simon L brings another great guest onto The CISO Experience podcast, Phosphorus Chief of Security Brian Contos! Watch the video recorded live below.
New Partnership Addresses the Region’s High Demand for xIoT Attack Surface Management and Remediation Capabilities NASHVILLE, TN – Phosphorus, the leading provider of advanced and full-scope security for the...
Over at Help Net Security, Phosphorus CSO Brian Contos defines xIoT before explaining how attackers view these devices. In this Help Net Security video, Brian Contos, CSO at Phosphorus...
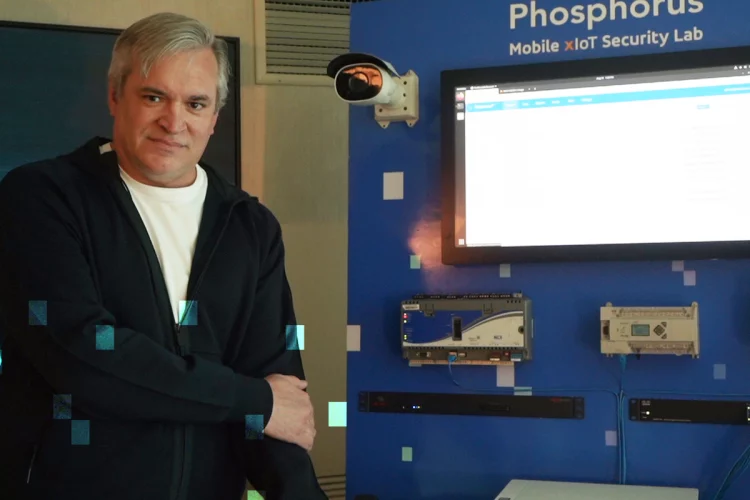
Nashville, Tenn. – Phosphorus Cybersecurity™, the leading provider of advanced and full-scope security for the extended Internet of Things (xIoT), is debuting the industry’s first Mobile xIoT Lab at...
An excerpt from Reader’s Digest‘ article, “8 Common Zelle Scams to Watch Out For” with comments from Phosphorus Chief Security Officer Brian Contos Zelle is a P2P (peer-to-peer) system...
An excerpt from Expert Insights‘ article, “Interview: How—And Why—Businesses Should Secure Their IoT Devices” with Phosphorus CEO Chris Rouland In recent years, the network perimeter has moved, with many...
So many IoT devices – cameras, printers, door locks, backup power and so much more, collectively bringing powerful capabilities to the enterprise. Excellent for enterprises, but attackers love IoT...
Published July 8, 2022, on CyberNews.com, Chief Security Officer Brian Contos describes what Apple’s new Lockdown Mode does and doesn’t do. While additional security measures are an important step in...
Published June 23, 2022, on DarkReading.com, Chief Security Officer Brian Contos writes on the prevention of these attacks, which must involve complete visibility into, and access and management over,...