Know your xIoT risk.
Eliminate the unknowns.
State of xIoT
Vulnerability assessment
Assess xIoT estates for password, firmware, certificate, configuration, and device state vulnerabilities automatically at-scale.
Real-world example

Ransomware targets Healthcare organizations
In 2024, nearly 400 U.S. healthcare organizations reported incidents linked to ransomware operators like LockBit 3.0, ALPHV/BlackCat and BianLian1
State of vulnerability assessment:

Attacks are accelerating
Over 820,000 IoT attacks per day were observed in 2025 — a 46% increase year-over-year. Threat actors are actively targeting connected devices at unprecedented scale.2

Unknown devices.
Unmanaged risk.
Unmanaged and misconfigured xIoT devices create security blind spots. Default credentials, outdated firmware, and poor hygiene make them easy entry points for attackers.

Breaches are costly
According to Forrester, 34% of IoT breaches result in $5–10M in losses — significantly higher than typical IT incidents due to operational disruption and downtime.3
The Phosphorus solution
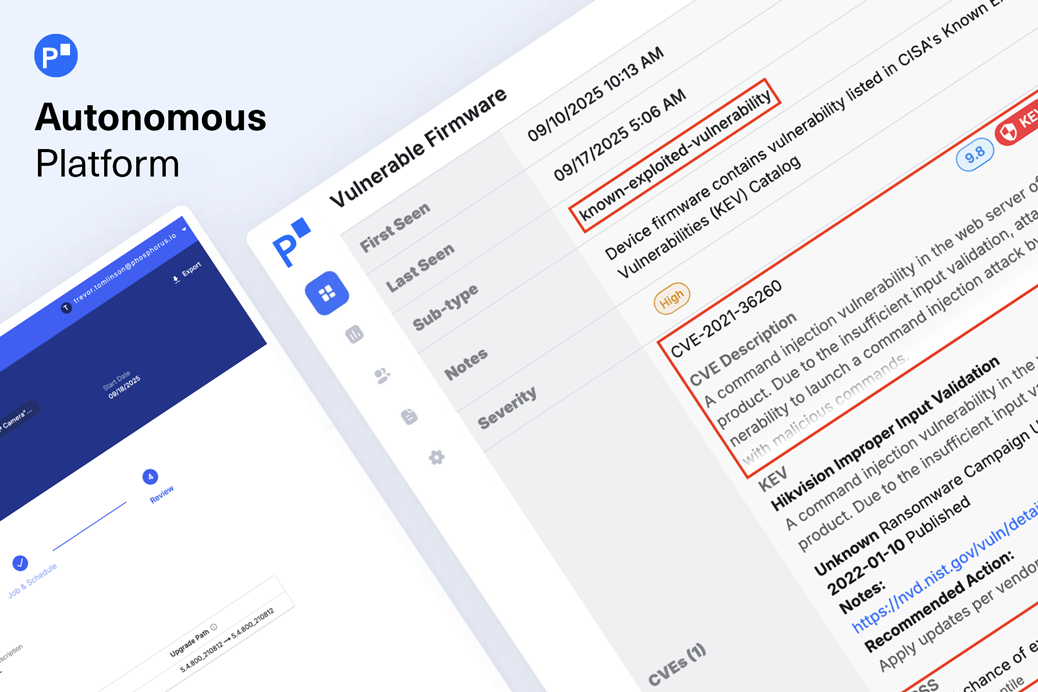
Vulnerability assessment must go beyond surface scanning
01
Deep xIoT risk intelligence

02
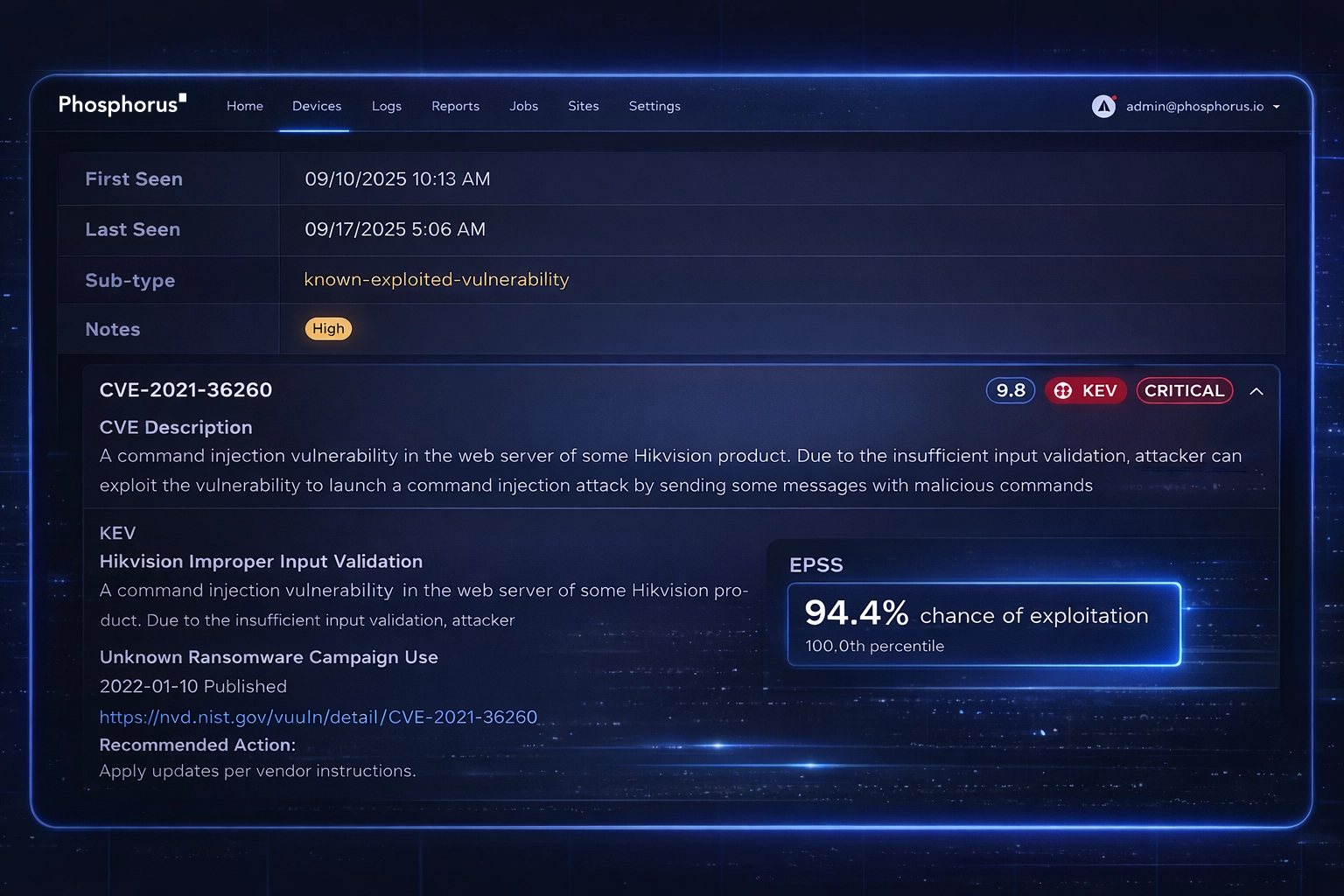
Exploit-aware vulnerability prioritization
Not all vulnerabilities pose equal risk. Enrich CVEs with intelligence from CISA’s Known Exploited Vulnerabilities (KEV) catalog and FIRST’s Exploit Prediction Scoring System (EPSS) to prioritize remediation based on real-world exploit likelihood, not just severity scores.
03
Compliance-ready reporting built in
Simplify regulatory alignment with built-in reporting mapped to NIST 800-53, NIST 800-82, IEC 62443, NERC CIP, HIPAA, NDAA Section 889, NIS2, and OTCC. Generate audit-ready documentation while maintaining operational visibility.

Not all vulnerability assessment is equal
From static CVE lists to exploit-aware risk intelligence
VULNERABILITY INSIGHTS
Latest on xIoT vulnerability assessment
Are you ready to see
Phosphorus in action?
Request a demo to learn how we can help you eliminate the xIoT security gap with the only IoT, OT, and IoMT discovery and remediation platform.