Automatically harden and remediate xIoT devices
What we do

Discover & assess
Safely discover, classify, and assess all xIoT devices in minutes, with no expensive hardware, SPANs, TAPs, or packet brokers.

Monitor & manage
Continuously monitor and manage all xIoT devices, while detecting and responding to device drift.
Credentials
xIoT password management
Enforce password standards across all devices.
- Automatically removes default and weak xIoT passwords, closing a common attack entry point.
- Enforces secure, automated password rotation at scale without disrupting operations.
- Reduces attack surface and improves compliance with centralized visibility and governance.

Devices still using default
manufacturer credentials1
0%
Firmware
xIoT firmware management
Keep firmware current, safely.
- Automatically discovers firmware risks across all xIoT devices, with CVE, KEV, and EPSS context.
- Safely automates firmware upgrades and rollbacks at scale without operational disruption.
- Automates firmware updates with policy-driven, scheduled upgrades and downgrades at scale.
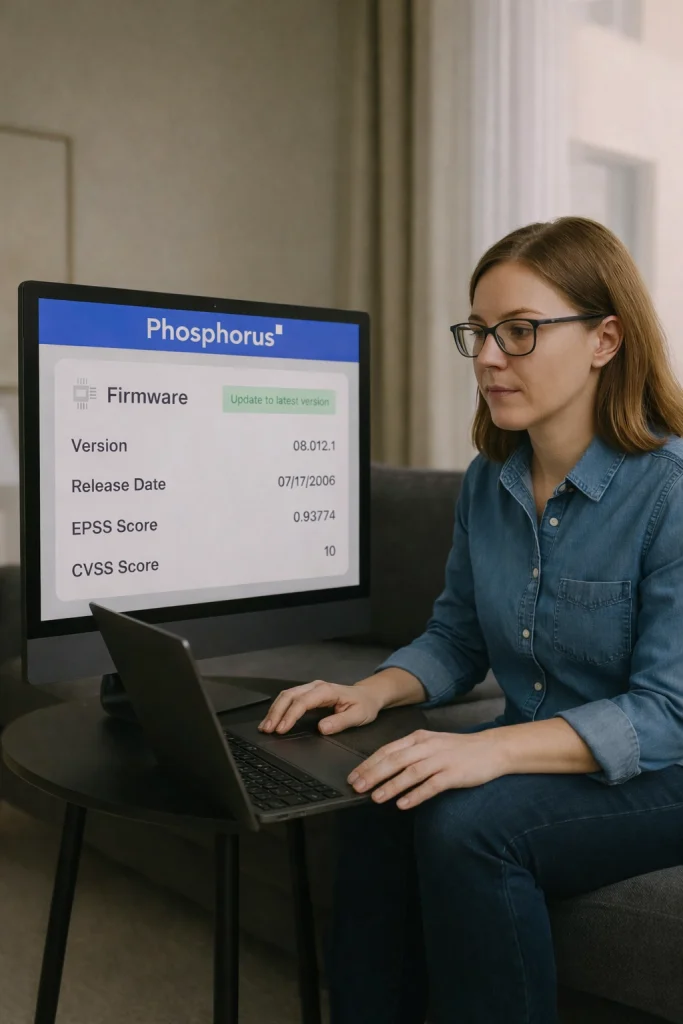
Devices run vulnerable
or outdated firmware2
0%
Certificates
xIoT certificate management
Enforce trusted identity across every device.
- Automatically discovers certificate risks across xIoT devices, including expired, self-signed, or misconfigured certs.
- Automates certificate deployment and renewal at scale, enforcing consistent, trusted identities.
- Strengthens authentication while reducing attack surface and overhead through centralized certificate governance.
- Extends Microsoft Active Directory and CyberArk Machine Identity (Venafi) certificate authority to xIoT devices.
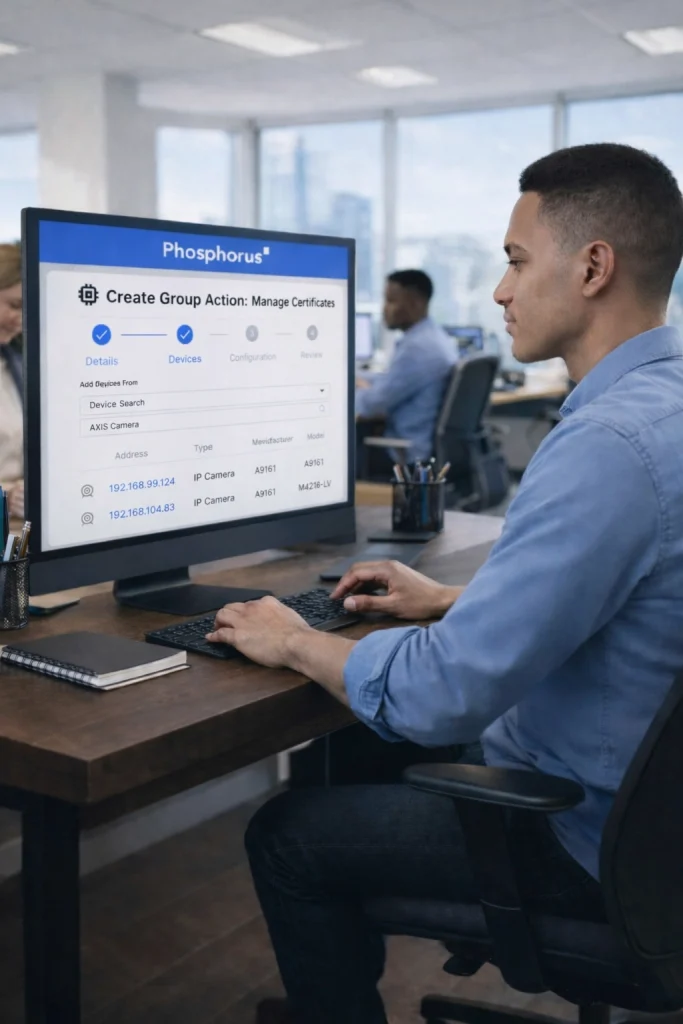
Devices operate with expired or unmanaged certificates3
0%
Configurations
xIoT configuration management
Enforce a secure, consistent posture across every device.
- Remotely disables unnecessary and insecure network services, such as Telnet and FTP, to reduce device attack surface and enforce secure configurations.
- Remotely configures and executes custom, device-specific actions at scale to securely manage diverse xIoT environments without manual intervention.
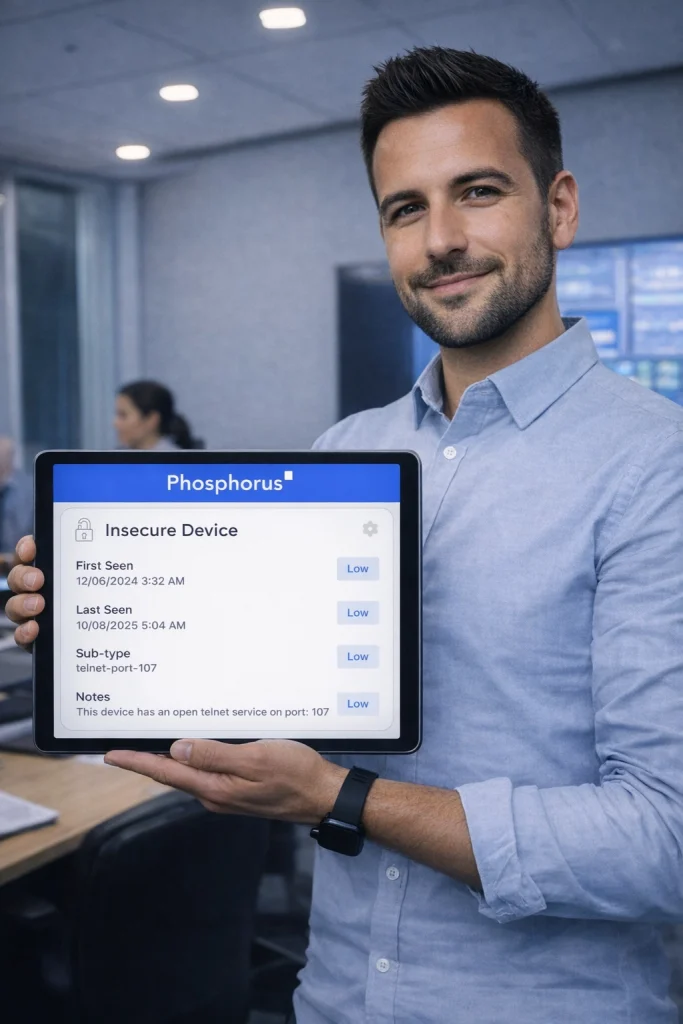
Devices running with
misconfigurations4
0%
Proven performance
Built for speed. Proven for accuracy. Designed for safety.

Fast deployment
4–12 minutes across real customer environments.
Validated across global healthcare, data centers, financial services, manufacturing, hospitality, food services, and government environments.

97% device classification rate
High-fidelity fingerprinting and protocol-level classification reduce false positives and unknown devices.

Zero-disruption discovery
- 100% safe for OT/IoMT/IIoT/ICS/IoT environments
- Tiered discovery agendas
- No reckless scanning
Sources
- 1 https://cert.pl/uploads/docs/CERT_Polska_Energy_Sector_Incident_Report_2025.pdf
- 2 https://phosphorus.io/how-akira-ransomware-camera/
- 3 https://www.datacenterdynamics.com/en/news/spacex-starlink-outage-caused-by-expired-ground-station-certificates/
- 4 https://www.scworld.com/news/suspected-chinese-malware-operation-menacing-iot-devices-with-hiatus-rat
Are you ready to see
Phosphorus in action?
Request a demo to learn how we can help you eliminate the xIoT security gap with the only IoT, OT, and IoMT discovery and remediation platform.

