Eliminate exploitable weaknesses.
Keep firmware current, safely.
State of xIoT
Firmware hygiene
Outdated firmware exposes xIoT devices to known exploits, enabling compromise and lateral movement across environments.
Real-world example
Vulnerable firmware facilitates Akira ransomware deployment via IP Camera
Exploitation of outdated firmware on an IP camera allowed Akira ransomware to infect an organization even after it was blocked by EDR on Windows systems.1
State of firmware hygiene:

Traditional tools fall short
Traditional vulnerability management tools are not designed for xIoT firmware visibility across diverse manufacturers and device types.

Lack of risk context
Vulnerability scanners lack exploitability and operational context, making it difficult to prioritize firmware remediation effectively.

Manual patching does not scale
Manual firmware updates cannot keep pace with xIoT scale and complexity, leaving critical vulnerabilities unaddressed.
The Phosphorus solution
Firmware management must move beyond manual patching
01
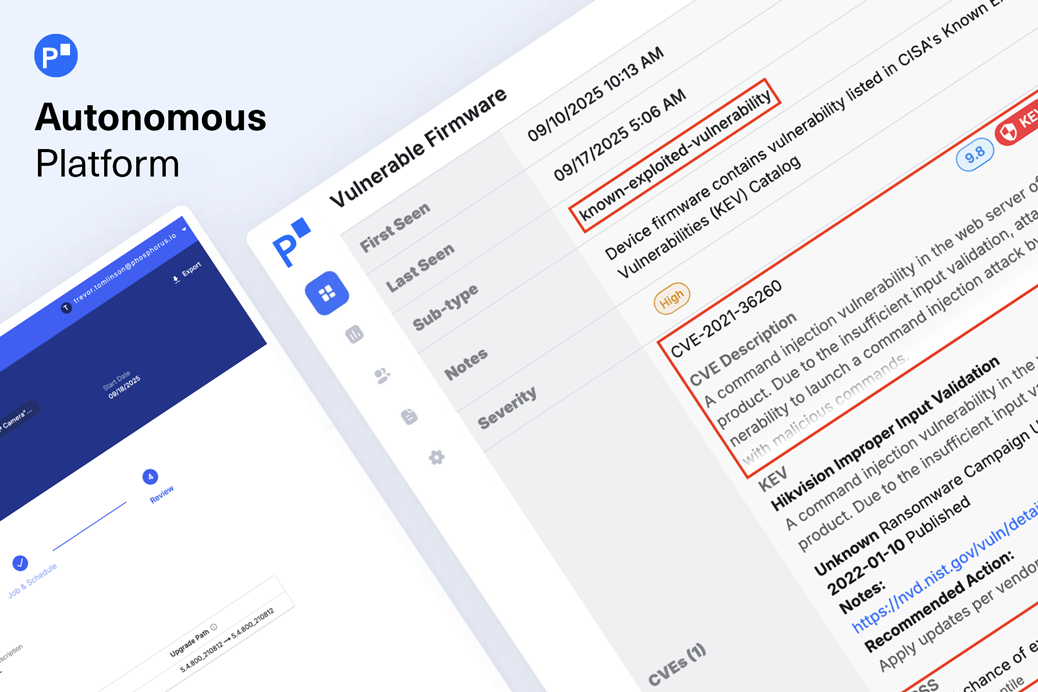
Identify firmware risk

02
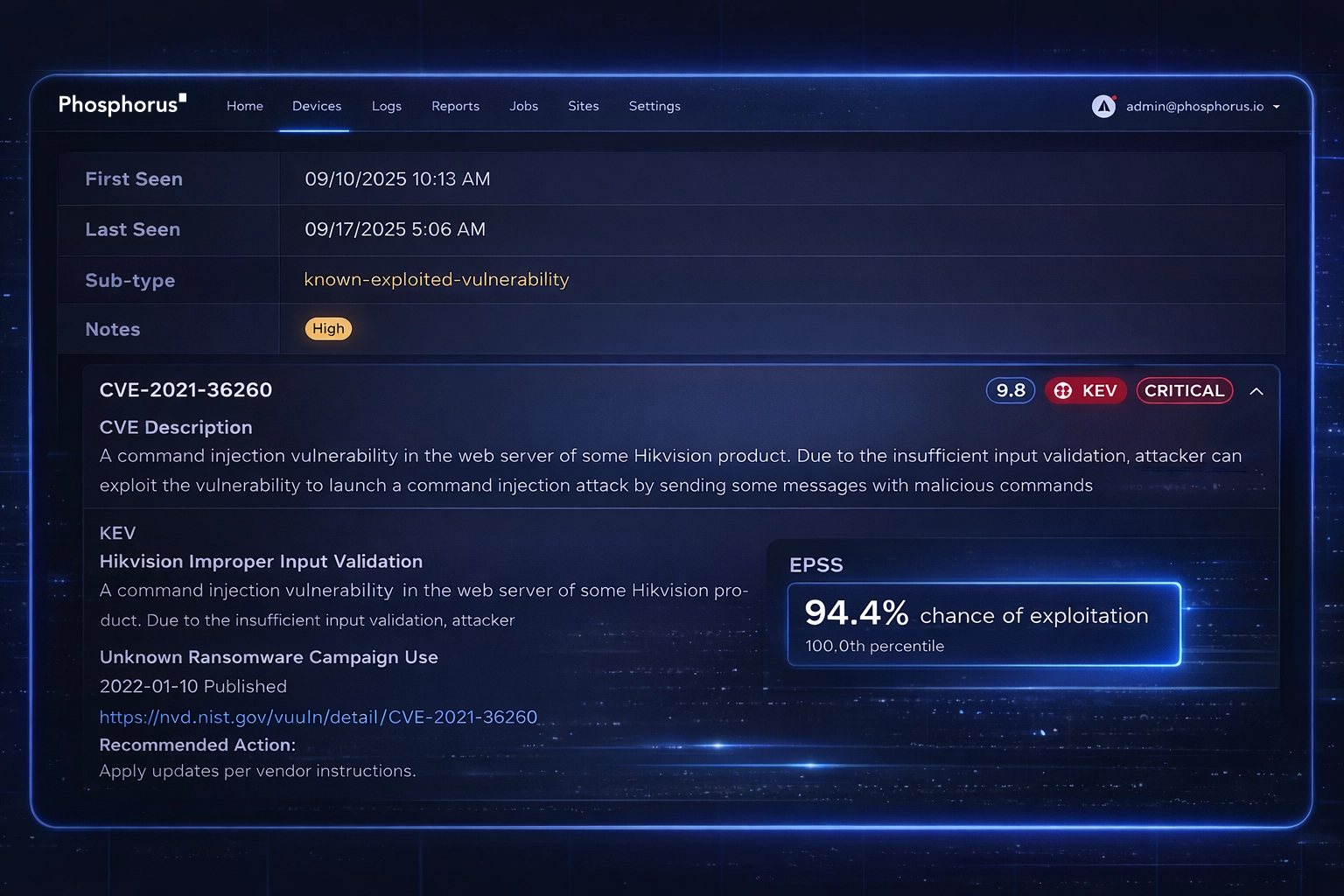
Prioritize real threats
Enrich firmware vulnerabilities with real-world exploit intelligence, including CISA’s Known Exploited Vulnerabilities (KEV) and Exploit Prediction Scoring System (EPSS) scoring. Focus remediation efforts on vulnerabilities that are actively exploited and most likely to impact your environment.
03
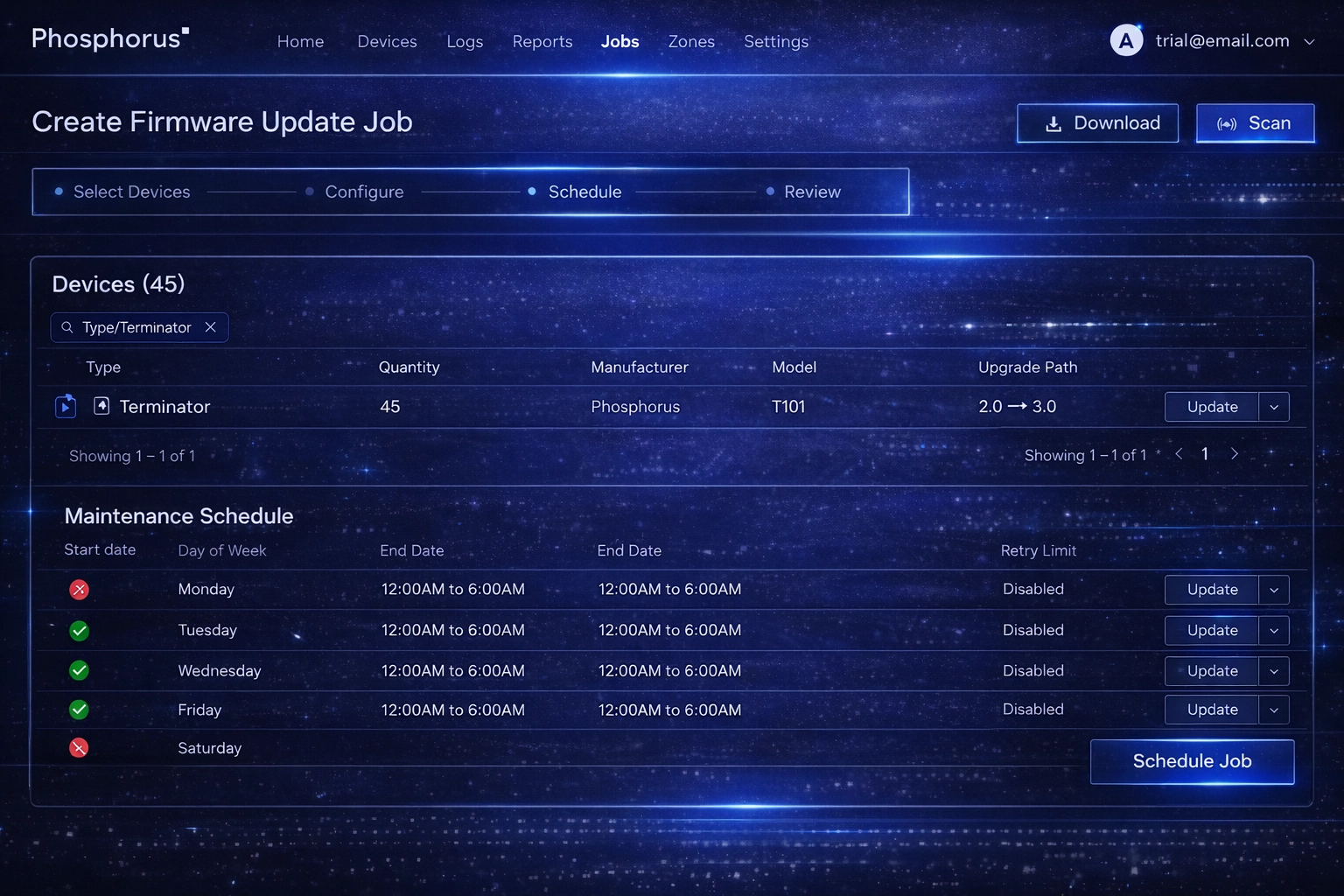
Automate safely at scale
Execute firmware upgrades and downgrades across thousands of devices using policy-driven scheduling and device-native methods. Ensure safe updates with rollback support and zero operational disruption.
Not all firmware management is equal
From manual firmware updates to automated xIoT firmware management
FIRMWARE INSIGHTS
Latest on xIoT firmware risk and management
Are you ready to see
Phosphorus in action?
Request a demo to learn how we can help you eliminate the xIoT security gap with the only IoT, OT, and IoMT discovery and remediation platform.