Eliminate certificate risk.
Enforce trusted identity.
State of xIoT
Certificate hygiene
Expired or self-signed certificates create security gaps, enabling unauthorized access, data exposure, and service disruption.
Real-world example

Expired certificate causes global outage
A global service disruption occurred when an expired certificate on a ground station caused widespread connectivity issues.1
State of certificate hygiene:

Causes outages and downtime
Certificate failures can break connectivity and disrupt critical systems and operations.
Exposes sensitive data
Weak cryptography and self-signed certificates weaken encryption, leaving communications vulnerable to interception.
Enables unauthorized access
Expired and self-signed certificates allow attackers to gain access and move laterally across networks.
The Phosphorus solution
Move beyond manual certificate management
01
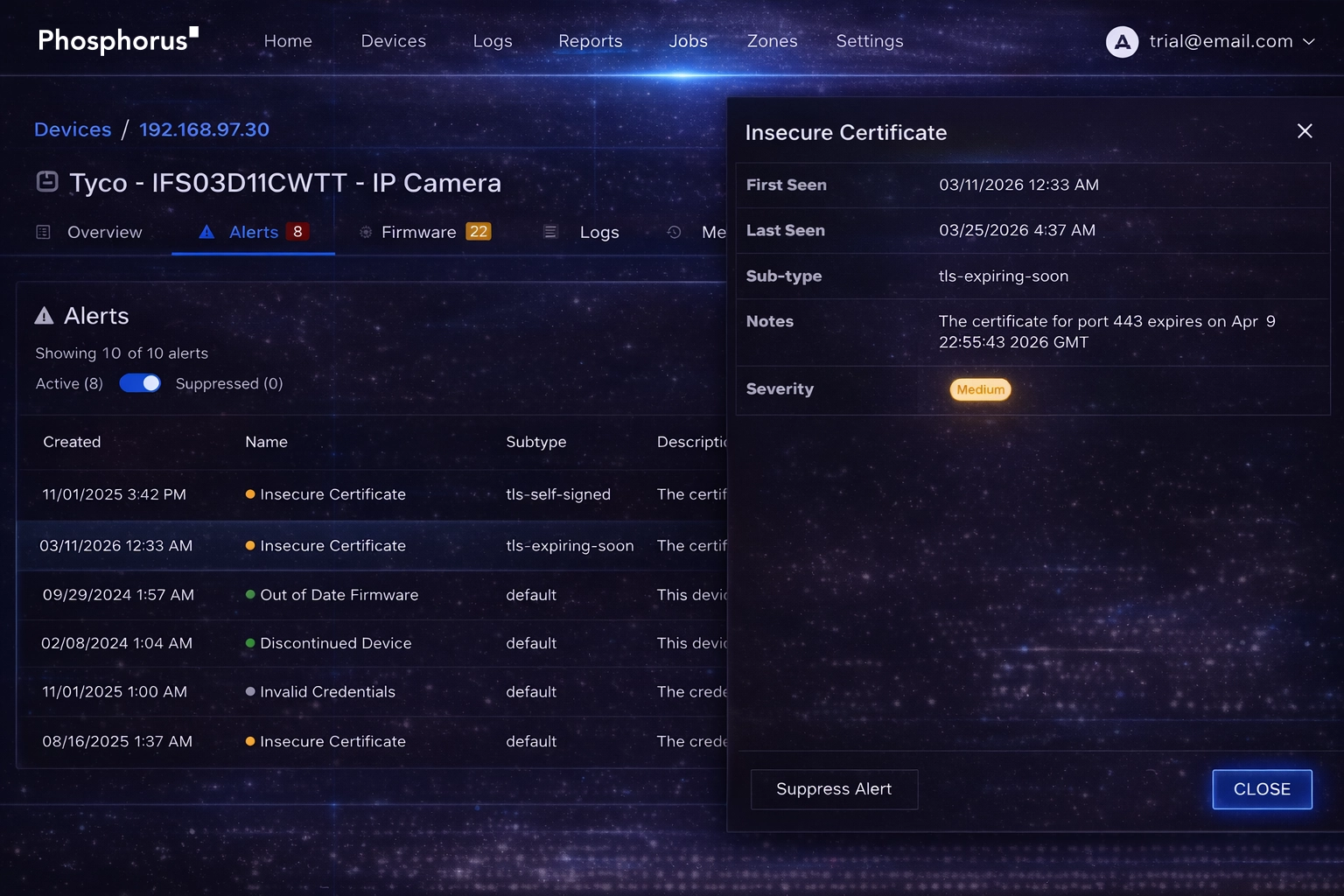
Identify certificate risk
Continuously discover certificates across all xIoT devices, including expired and self-signed certificates. Gain full visibility into certificate health and device identity across your environment.

02
Extend Certificate Management to xIoT
Extend CyberArk Machine Identity (formerly Venafi) and Microsoft Active Directory Certificate Services to IoT and OT devices. Ensure consistent, trusted authentication across your environment with centralized certificate control.
03
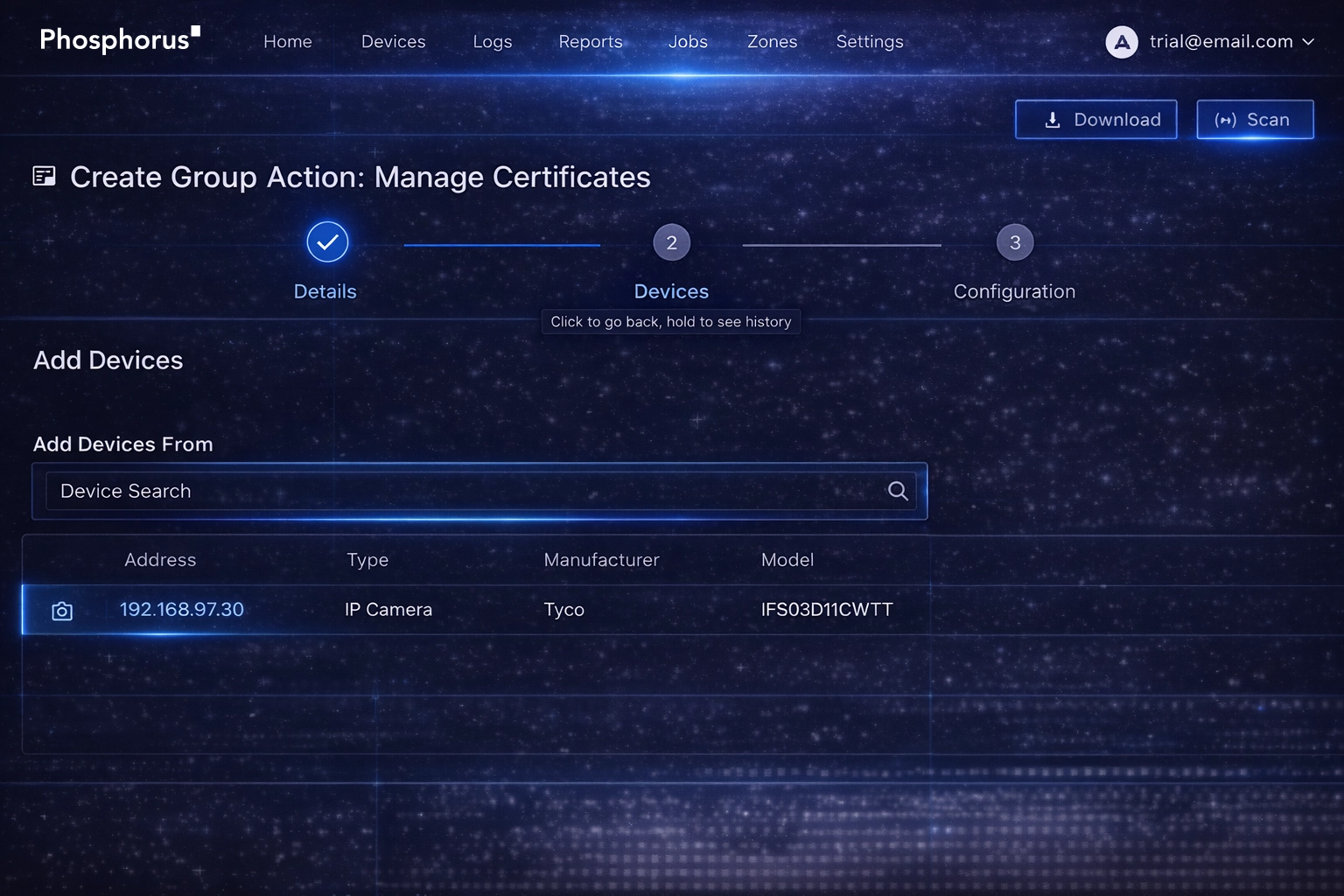
Automate certificate lifecycle
Automate certificate generation, installation, and renewal at scale using policy-driven workflows. Reduce manual effort while strengthening security and maintaining continuous device trust.
Not all certificate management is equal
From manual certificate handling to automated xIoT identity management
CERTIFICATE INSIGHTS
Latest on xIoT certificate management
Are you ready to see
Phosphorus in action?
Request a demo to learn how we can help you eliminate the xIoT security gap with the only IoT, OT, and IoMT discovery and remediation platform.